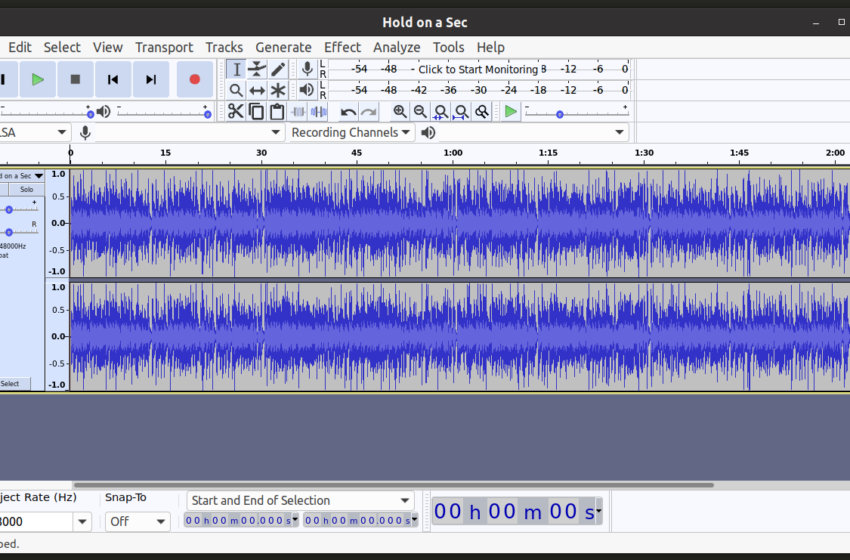
Audio editing software can help you refine your audio for better quality when listening. Whether you’re turning your voice into a pro recording or using […]
Category: Computer
IOS five Features – What Is the iMessage Feature All About?
iMessage is one of the cool new features to be had for iPad, iPhone, and iPod contact customers with the new iOS 5 software. This […]
The Many Benefits That iOS Apps Can Bring to Your Business
IOS Apps is everyone’s friend. If you think that iOS apps and their corresponding cell gadgets are too juvenile to your flavor, it is time […]
5 Essential Qualities to Expect in an Adroit iOS App Developer
With the call for iPhones reaching its peak, most agencies are drawing their shift toward building pinnacle-rated iOS apps, which will widen their customer base. […]
Five Reasons Why iOS Is Superior to Android
Upon its release, Google’s Android platform was predicted to overhaul Apple’s iOS in both capability and recognition. While some may argue the former expectation was […]
Features Of Android And IOS
iOS and Android are the two maximum famous and person-friendly working systems that are being used for cell gadgets. Both of these applications are filled […]
Top IOS Development Trends to Watch Out for in 2017 for Businesses
With most folks hovering over the Internet via our cell gadgets nowadays, agencies are pushing over to create an effect on the target audience this […]
Android Game Vs iOS Game Development
When it comes to deciding on a smart smartphone, one commonly has to pick among mobile gadgets helping predominant platforms – iOS and Android. The […]
How To Install Replacement Windows In Your Home
Installing alternative home windows in your property isn’t always an overcomplicated undertaking to accomplish; however, it has to be given an affordable amount of time […]
Apple IOS 5 for iPhone, iPad and iPod Touch Explained
Apple iOS five become introduced at the Worldwide Developers Conference in early June 2011. When released, it will be supported on the iPad, iPod, iPhone […]