Previous: DerpTrolling sports server DDoS attacker pleads responsible
Next: Sent an image to the wrong person? Facebook Messenger will let you unsend it
by John E Dunn.Researchers have published info of a dangerous flaw inside the way the hugely famous WooCommerce plugin interacts with WordPress that might permit an attacker with access to a single account to take over a whole website online.
WooCommerce’s 4 million-plus users were first alerted to the problem some weeks again inside the release notes for the up-to-date model:
Versions three.4.Five and in advance are affected by a handful of problems that permit Shop Managers to exceed their abilties and perform malicious actions.
This week, PHP safety organization RIPS Technologies published the studies that led to this warning which gives WooCommerce and WordPress admins extra of the gory detail.
There are elements to the vulnerability, the first of which the researchers describe as a “layout flaw in the privilege system of WordPress.”
The second, in WooCommerce itself, is a reputedly easy record deletion vulnerability affecting variations 3.4. Five and in advance.
Which of the 2 is the larger issue will rely upon whether or not you worry more approximately a site’s e-commerce feature or show up to be its admin – in both manners, the aggregate spells trouble.
After gaining admission through a phishing assault or as an internal process, an attacker could use a weak spot inside the log file deletion routine to delete woocommerce.Php, taking down the website and inflicting WordPress to disable the plugin.
This, RIPS Technologies researcher Simon Scannell discovered, might be enough for any WooCommerce person with a Shop Manager account and an information of what they’d just executed to compromise the entire web page.
But how?
When WooCommerce is installed, the Shop Manager role is assigned the robust edit_users capability needed to edit purchaser debts, that’s saved with the aid of WordPress itself.
Because this will be used to edit the WordPress web site’s admin account too, its scope is restricted by way of a unique WooCommerce ‘meta capability’ filter out.
Unfortunately, for WordPress to use this shield the plugin wishes to be energetic – which it wouldn’t be if an attacker has exploited the WooCommerce document deletion weakness.
Writes Scannell:
The meta privilege test which restricts shop managers from editing administrators might not execute and the default conduct of allowing users with edit_users to edit any user, even directors, could occur.
The WooCommerce account with Shop Manager privileges would then be capable of raise those to alternate the site’s password and with it control of the entire web page.
What to do
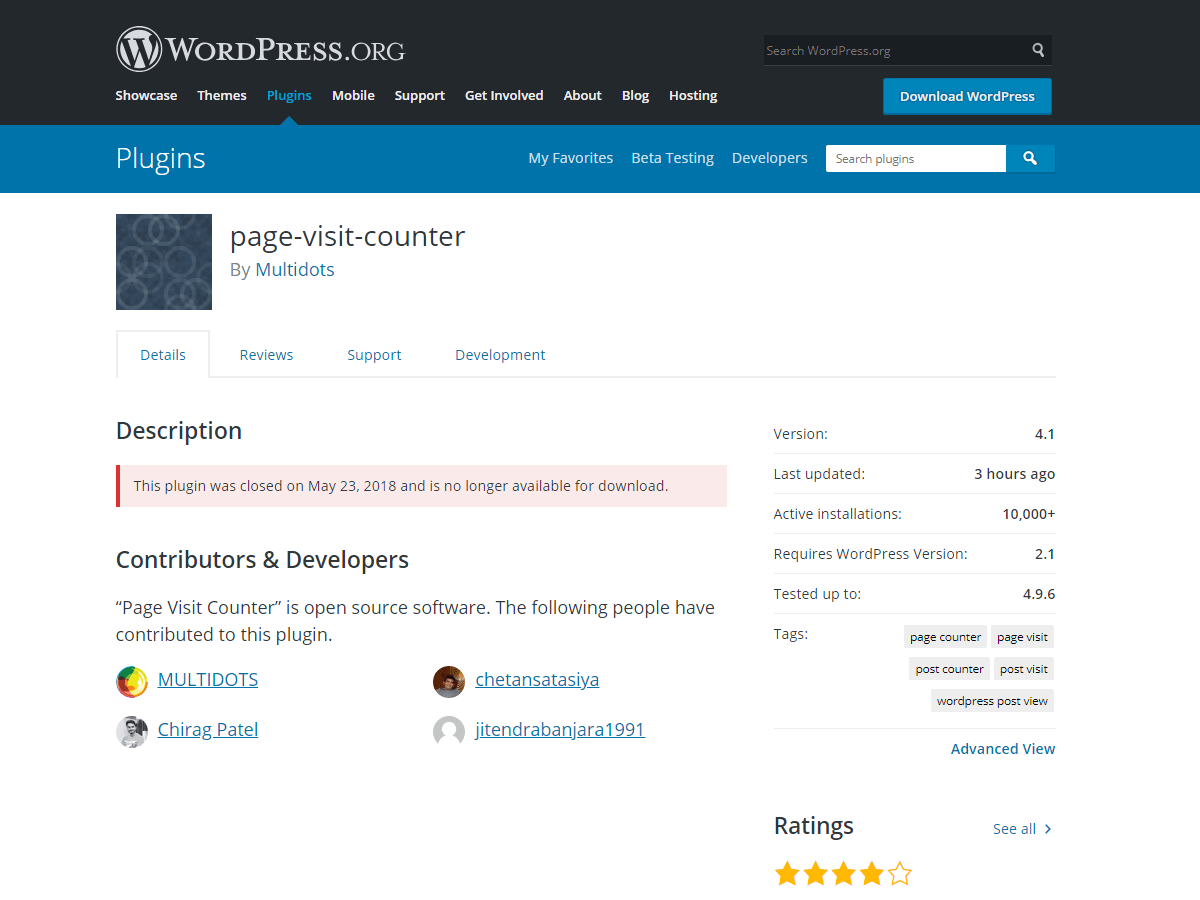
On the WooCommerce side, ensure it’s been upgraded to model three.Four.6, which regarded on eleven October. Plugins aren’t up to date by using the default, which means that admins will need to initiate this for themselves through the wp-admin dashboard/plugins sidebar.
As for the WooCommerce fix:
With this release, Shop Managers can handiest edit customers with the Customer position using the default, and there’s a whitelist of roles that Shop Managers can edit.
Redesigning the manner the WordPress permission system interacts with plugins would possibly take a little longer.
For motives as long as your arm, plugins have always been WordPress’s underbelly. The TL;DR is they want regular tending as does the platform itself – by no means take both without any consideration.
Although WordPress began out as a simple blogging device, today it has developed into an entire content material control device (CMS) that can be used no longer most effectively for running a blog but for nearly whatever, with millions of human beings the usage of it as a private or business internet site. This is typically due to the masses of plugins and widgets which might be available for use. The freedom that WordPress has as a self-hosted platform implies that you could use it to create any website, simple or complex, one-of-a-kind blogs, and so much more, at the same time as being noticeably easy to apply.
In order to acquire all this, WordPress uses many special plugins, specifically in terms of SEO. Search engine optimization (search engine optimization) is one of the maximum important gear used to boom traffic on an internet site.
One of the first-rate known plugins for SEO is the Yoast plugin. This plugin has over 14 million downloads as their internet site claims. It is an extensively uunfoldednotion that your WordPress website will in no way have sufficient seo (search engine optimization) if you do not have the WordPress search engine marketing with the aid of the oast plugin set up.
However, a huge flaw has been observed in this plugin that might position your website at risk and motivate the leakage of exclusive facts.
How comfortable is SEO through Yoast?
Last week, an important Yoast vulnerability has been observed which could have put thousands and thousands of websites at important chance to be attacked with the aid of hackers. This Yoast vulnerability became discovered by means of a developer of the WordPress vulnerability scanner Ryan Dewhurst, and it applies to almost every version of the plugins that move by using the name “WordPress search engine optimization via Yoast”.