Hackers have exploited –and are currently persevering with to exploit– a now-patched zero-day vulnerability in a popular WordPress plugin to install backdoors and take over sites.
The vulnerability affects WP GDPR Compliance, a WordPress plugin that allows website online owners to turn out to be GDPR compliant. The plugin is one of the most famous GDPR-themed plugins in the WordPress Plugins directory, with over a hundred,000 active installs.
Around three weeks ago, attackers appear to have found a vulnerability on this plugin and commenced the usage of it to gain access to WordPress websites and set up backdoor scripts.
Initial reports approximately hacked websites were made into any other plugin’s guide discussion board, however, that plugin became out to were hooked up as a 2nd-level payload on a number of the hacked websites.
After investigations led with the aid of the WordPress security group, the source of the hacks changed into eventually traced back to WP GDPR Compliance, which became the commonplace plugin set up on all said compromised websites.
The WordPress crew eliminated the plugin from the reliable Plugins listing earlier this week when they diagnosed numerous safety troubles inside its code, which they believed were the cause of the pronounced hacks.
The plugin was reinstated days ago, but best after its authors released model 1.4. Three, which contained patches for the reported problems.
ATTACKS ARE STILL GOING ON
But no matter the fixes, attacks on websites nonetheless going for walks versions 1.4.2 and older are still happening, in step with security experts from Defiant, a corporation that runs the Wordfence firewall plugin for WordPress sites.
The company’s analysts say they’re persevering to detect assaults that try to make the most of one of the suggested WP GDPR Compliance safety troubles.
In specific, attackers are targeting a WP GDPR Compliance bug that allows them to make a call to one of the plugin’s internal functions and exchange settings for both the plugin, but also for the entire WordPress CMS.
The Wordfence crew says they have got visible two forms of attacks through the use of this computer virus. The first state of affairs goes like this:
Hackers use the trojan horse to open the site’s user registration gadget.
Hackers use the trojan horse to set the default position for new accounts to “administrator.”
Hackers register a new account, which robotically becomes an administrator. This new account is usually named “t2trollherten.”
Hackers set lower back default consumer function for brand spanking new debts to “subscriber.”
Hackers disable public user registration.
Hackers log into their new admin account.
They then continue to install a backdoor at the website, as a report named wp-cache. Personal home page.
This backdoor script (GUI pictured underneath) incorporates a document supervisor, terminal emulator, and a PHP eval() function runner, and Wordfence says that “a script like this on a website can allow an attacker to set up similar payloads at will.”
But experts also detected a second type of assault, which does not rely on developing a new admin account, which is probably noticed via the hacked website’s owners.
This second and supposedly extra silent technique entails the use of the WP GDPR Compliance malicious program to add a new undertaking to WP-Cron, WordPress’ built-in undertaking scheduler.
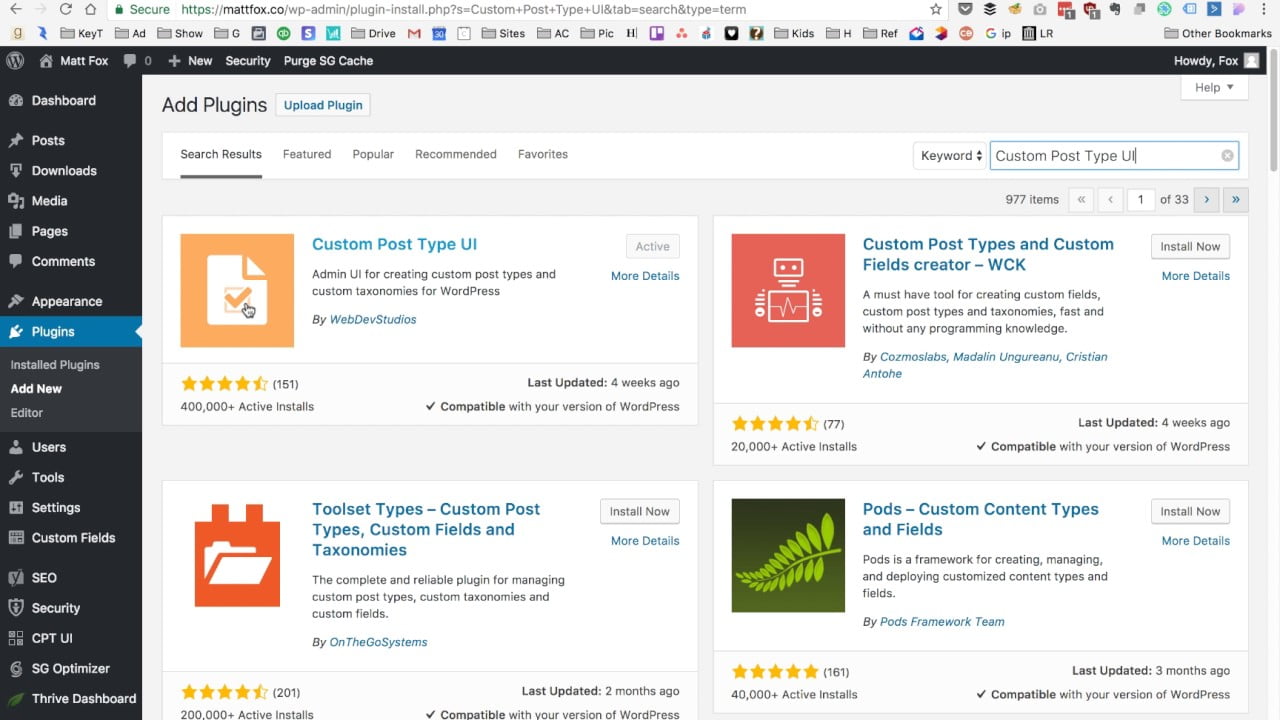
The hackers’ cron activity downloads and installs the 2MB Autocode plugin, which attackers later use to add some other backdoor script on the website online –also named wp-cache.Hypertext Preprocessor, but one-of-a-kind from the only specific above.
But whilst hackers tried to make this 2nd exploitation scenario greater silent than the primary, it became, in truth, this method that led to the 0-day’s discovery.
This passed off due to the fact, on some sites, the hackers’ exploitation habitual failed to delete the 2MB Autocode plugin. Site proprietors noticed a brand new plugin regarded on their websites and panicked.
It became, in truth, in this plugin’s WordPress assist forum that site owners first complained approximately hacked websites, and caused the research that led lower back to the WP GDPR Compliance plugin.
ATTACKERS ARE STOCKPILING HACKED SITES
Right now, the attackers do not appear to be doing something malicious with the hacked websites, in step with the Wordfence team.
Hackers are simply stockpiling hacked websites, and Wordfence has not seen them looking to deploy something malicious via the backdoor scripts, which include search engine optimization spam, taking advantage of kits, malware, or other types of badness.
Site ownerswhoe use the WP GDPR Compliance plugin nevertheless have time to replace or get rid of the plugin from their websites and clean any backdoors that have been left behind. They need to do this before their website takes a hit in phrases of search engine ratings, which generally happens after Google reveals malware on their domains at some point in its regular scans.